Zero Trust Security
- A more dynamic and adaptive way to handle security
- Protect against threats from both outside and inside your network
- Minimize the risk of unauthorized access and data breaches
Unify your network and IT infrastructure
Enhanced network security and resilience
Safely connect every person, device, and application
Join's zero trust framework allows you to verify and authenticate all users, devices, and applications, regardless of their location.
Flexible user authentication allows you to to integrate your existing identity service, such as SSO, pre-shared key (PSK), or MFA, for easy access.
Least-privilege access only grants access to the resources users absolutely need, limiting the potential damage in case of a security breach.
Micro-segmentation divides the network into smaller segments, allowing your business to isolate and protect sensitive data and applications from unauthorized access.
Continuous authentication requires re-authentication of user and devices periodically, to confirm the credentials and context of users, devices, and network traffic.
Reduce the risk of data breaches and cyberattacks
Our proactive and comprehensive approach to security helps protect your critical assets and sensitive data for a more secure and resilient network environment.
Join's network architecture is engineered to treat every access request as if it's coming from an untrusted network.
Enterprise authentication allows you to track all usage of your network and remove access using your global user store.
Network dashboard and analytics monitors who is using your data and when – sending alerts to our network operation center (NOC) when inappropriate access is detected.
Network as a Service
Explore all the benefits of Join NaaS
Cloud Wired + Wireless LAN
Turnkey cloud-managed networks, inclusive of hardware, software, design, installation, maintenance.

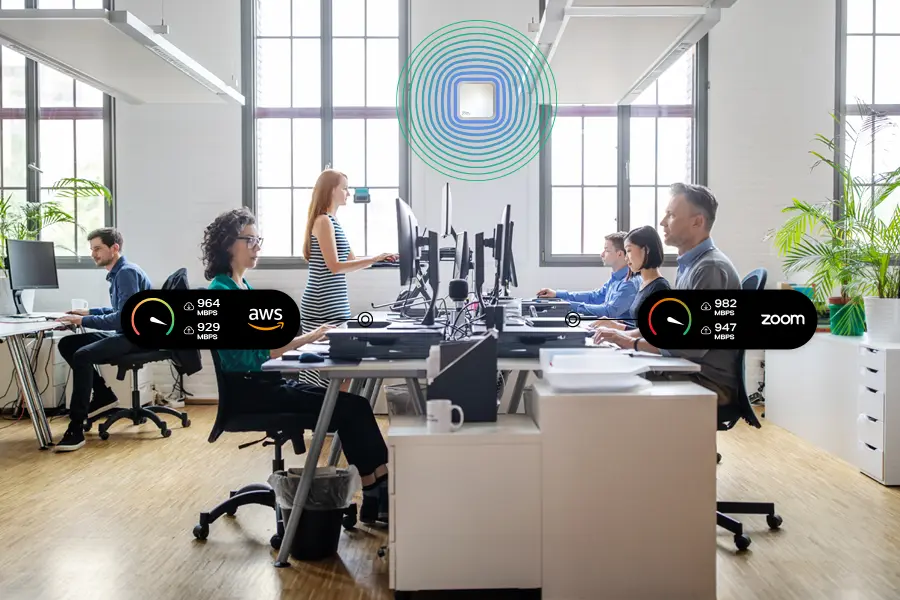
Managed WAN and Business Internet
Fast, redundant connectivity optimized for optimal performance to every device and application.

Network Performance + Analytics
High uptime and guaranteed SLAs with our redundant network design, active performance monitoring and optimizations.
Getting a fast, secure, reliable network experience is easier than you think
We make it easy to quickly deploy your entire network and IT infrastructure, from routing, switching, access points, firewalls, and secure connectivity.
- Ultra fast business Internet
- Reliable wired and wireless networking
- Zero Trust security
- Proactive network monitoring and optimization
- 100% as a service... turnkey installation, zero CapEx, zero-touch provisioning.